Trezor Login — Your Digital Fortress for Crypto Security
Stay in control of your cryptocurrency journey with Trezor Login — a hardware-protected, privacy-first method of accessing your digital wealth safely and efficiently.
What is Trezor Login?
The Trezor Login process is the secure method users employ to access their crypto assets stored on Trezor hardware wallets. It eliminates the need for conventional passwords and ensures that private keys never leave the device, offering complete protection from phishing, malware, and unauthorized access.
Trezor’s design philosophy is simple — “Your keys, your coins.” When you log in, the verification occurs entirely within your hardware device, not on your computer or the internet. This means even if your computer is compromised, your crypto remains untouched.
How to Log in to Your Trezor Wallet
1. Connect Your Device
Use the original USB cable to connect your Trezor hardware wallet to your computer. Ensure the Trezor Bridge software is installed for smooth communication.
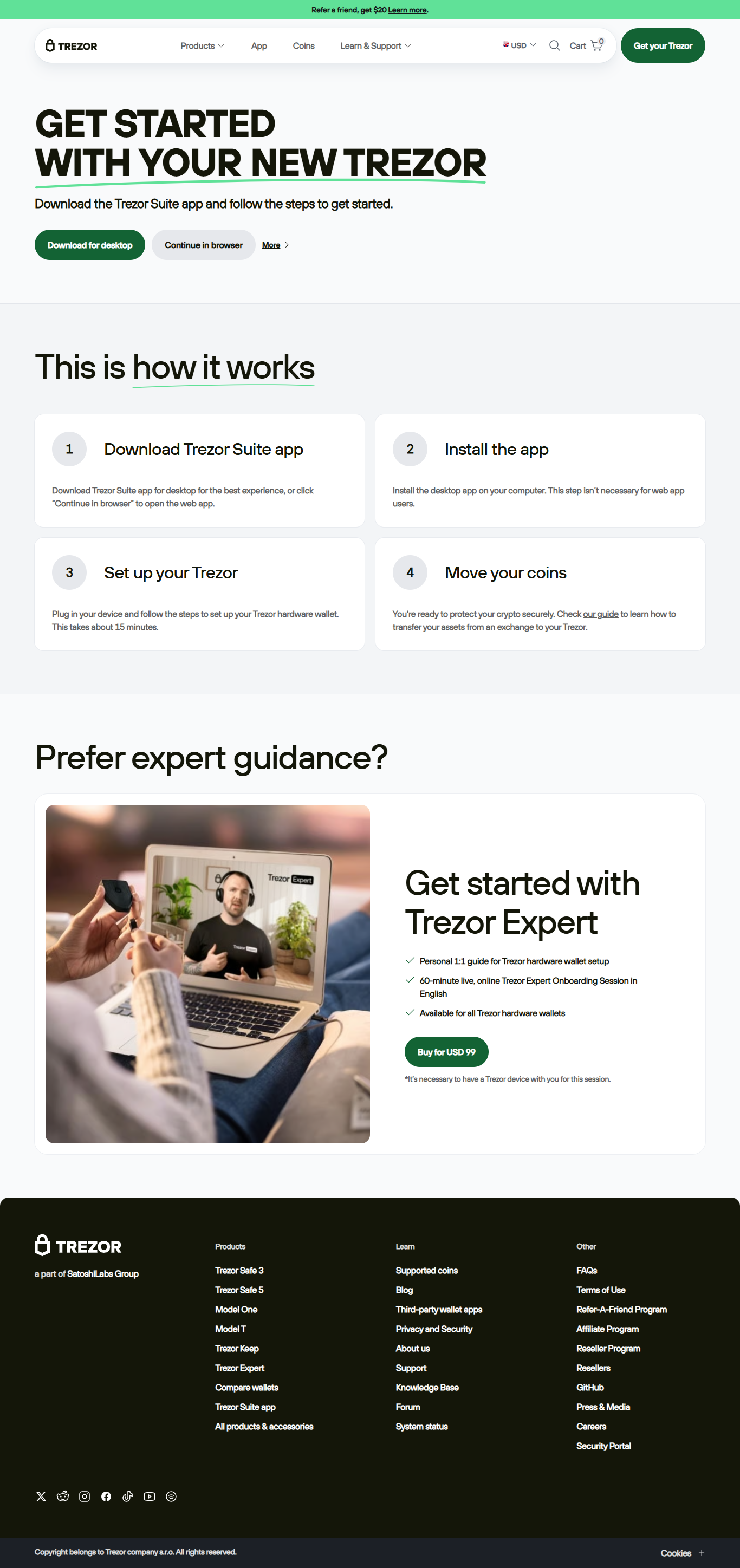
2. Visit Trezor Suite or trezor.io/start
Access the official Trezor platform through Trezor Suite or the verified URL. Always type it manually to avoid fake sites.
3. Authenticate via PIN
Enter your PIN directly on the device screen. This ensures no keylogging or data capture can occur on your computer.
4. Manage Your Portfolio
After successful login, your dashboard displays balances, transaction history, and portfolio analytics — all secured locally.
Why Trezor Login is the Gold Standard in Crypto Security
- Offline Authentication: Your private keys remain offline, shielded from online breaches.
- Human Verification: Every transaction must be confirmed manually on your device’s screen.
- Firmware Protection: Only official Trezor firmware can run, preventing tampering.
- Open Source Transparency: Trezor’s code is public, ensuring full accountability and trust.
Trezor Login vs Traditional Wallet Access
| Feature | Trezor Login | Online Wallet Login |
|---|---|---|
| Private Key Access | Stored offline | Stored on web servers |
| Login Method | PIN + Hardware Verification | Password only |
| Phishing Protection | Built-in and visual confirmation | Vulnerable to fake sites |
| Device Requirement | Trezor Hardware Wallet | Browser/Cloud access |
“With Trezor Login, your crypto never leaves your hands — it’s like having a vault you can carry in your pocket.”
Common Trezor Login Issues and Fixes
- Device Not Detected: Reconnect your Trezor, use a different USB port, or reinstall Trezor Bridge.
- Suite Not Loading: Update to the latest Trezor Suite version and restart your browser.
- Forgotten PIN: You can reset the device and recover using your seed phrase.
- Firmware Update Stuck: Disconnect and retry in bootloader mode for a clean installation.
Frequently Asked Questions About Trezor Login
1. Can I log in to Trezor without the hardware device?
No, your Trezor wallet is required for every login to verify your identity securely.
2. Is it safe to use Trezor Login on a public computer?
Yes, since all sensitive actions occur inside the device, not on the computer itself.
3. What if my Trezor is lost or damaged?
You can restore access on a new device using your recovery seed phrase.
4. Does Trezor Login support multiple crypto assets?
Yes, it supports Bitcoin, Ethereum, and hundreds of other digital currencies through Trezor Suite.
Your Crypto, Your Rules — With Trezor Login
The Trezor Login system is built for crypto enthusiasts who prioritize safety and autonomy. By bridging ease-of-use with offline hardware protection, it ensures every login is a step toward digital independence and peace of mind.
© 2025 Trezor Login | Secure. Verified. Trusted.